Infrastructure Access¶
For Blotout to access your AWS account we require access keys and secret keys. The keys are passed in the terraform script which provisions the infrastructure in your AWS account. Click here to know how to create a user and generate its keys if you don't have any user created. It is a good practice to create a different user for blotout deployment though you can use an already existing user by attaching the required policies.
By default we are not attaching any permissions to the user in Creating AWS user step. To simplify the onboarding process you can attach the Administrator Access policy to grant admin access to the user. If you don't want to allow admin access you can attach the following restrictive restrictive policies to the user.
Note
Either one of the admin access or the restrictive policies must be attached to the user
Creating AWS user¶
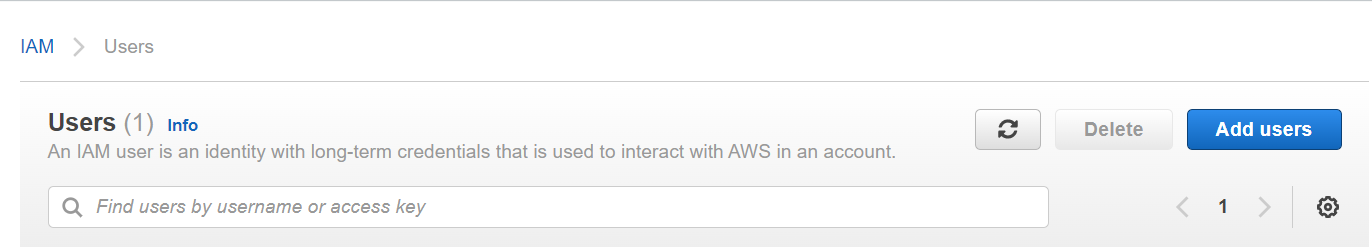
- Go to the AWS console and then click IAM.
- In this click on Add Users.
- Give the username and Select Access key - Programmatic access.
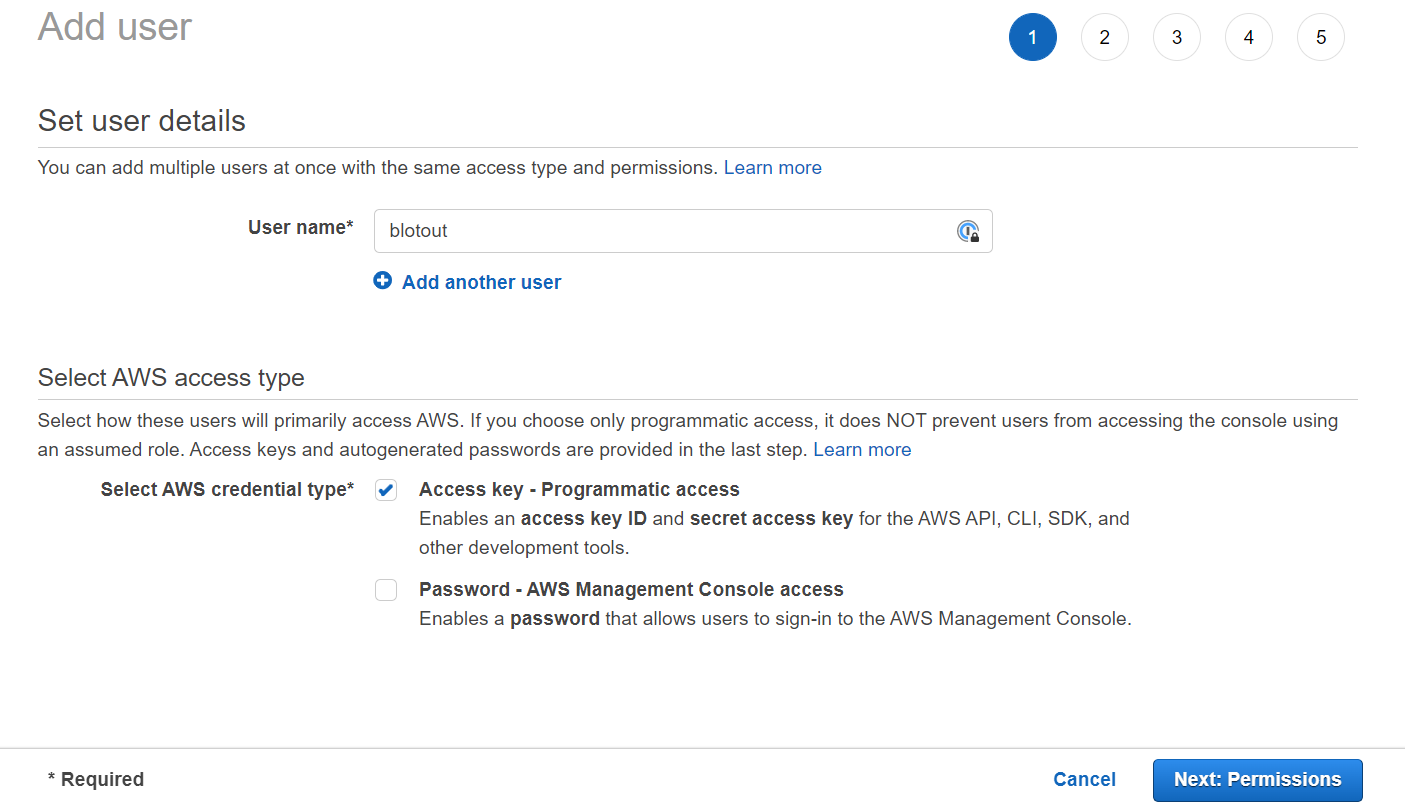
- Click on Next: Permissions.
- Don't add any permissions here.
- Click on Next: Tags. Give any tags if you want to otherwise click on Next: Review.
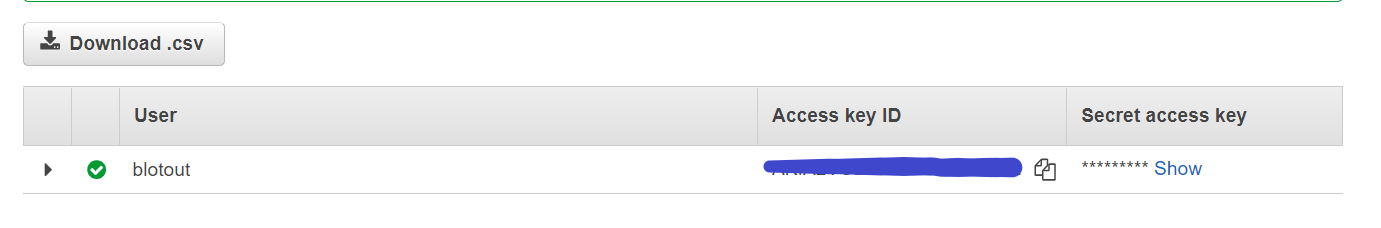
- In the next step click on Create User.
- On the next page you will have Access key and Secret key. Copy the credentials and store them somewhere safe.
Attaching Admin access to the user¶
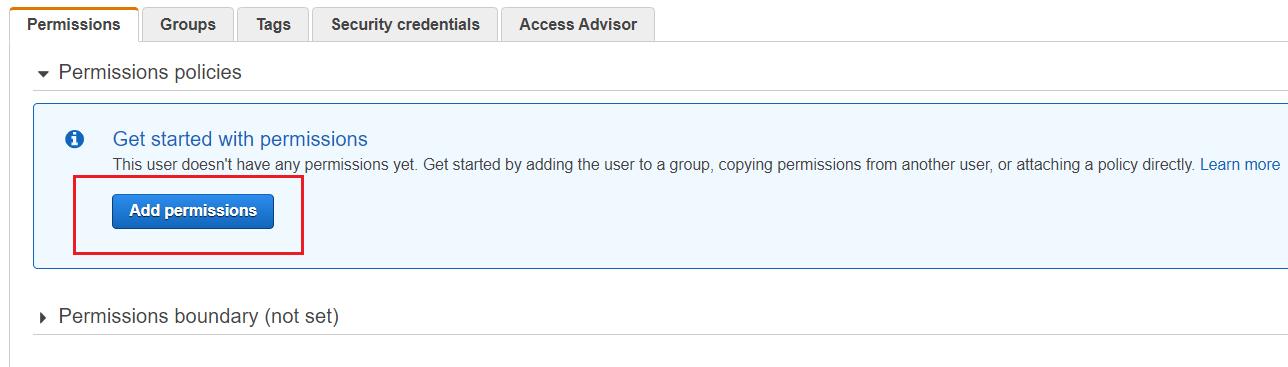
- Go to IAM and then click on Users.
- Click on the user you created above.
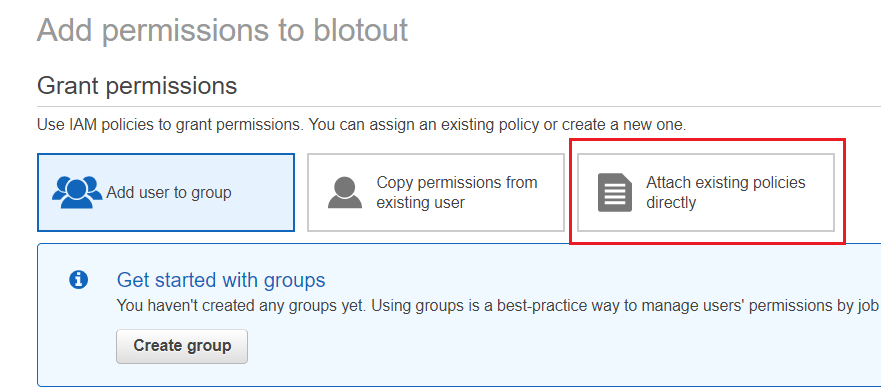
- Click On Add Permissions.
 .
. - Select Attach existing policies directly.
 .
. - Select AdministratorAccess and then click on Next: Review.
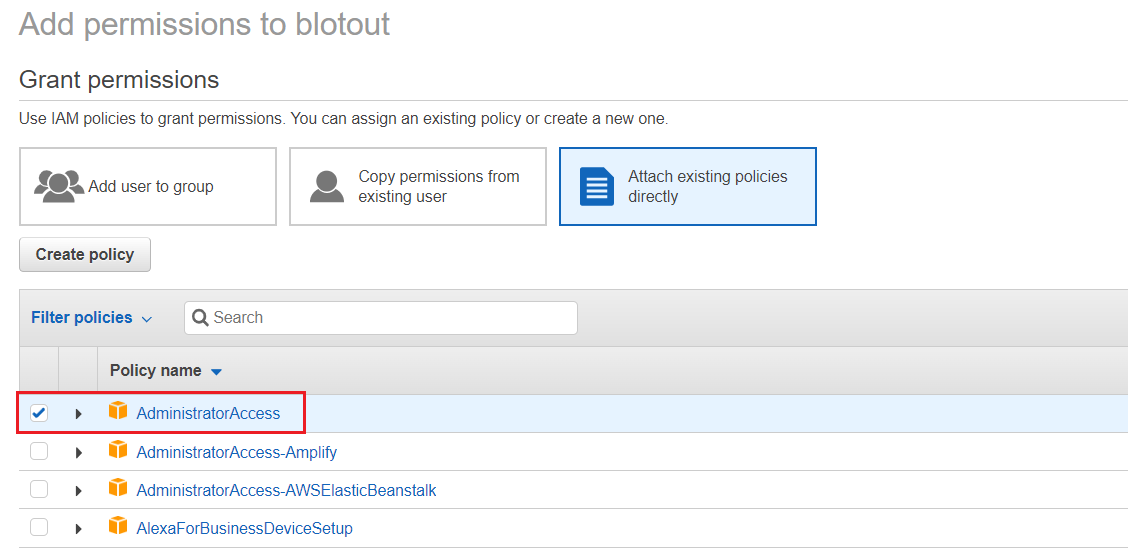 .
. - Click on Add permissions to attach the selected policy.
Creating IAM policy¶
- Go the AWS console and click on IAM.
- Go to Policies and click on Create Policy.
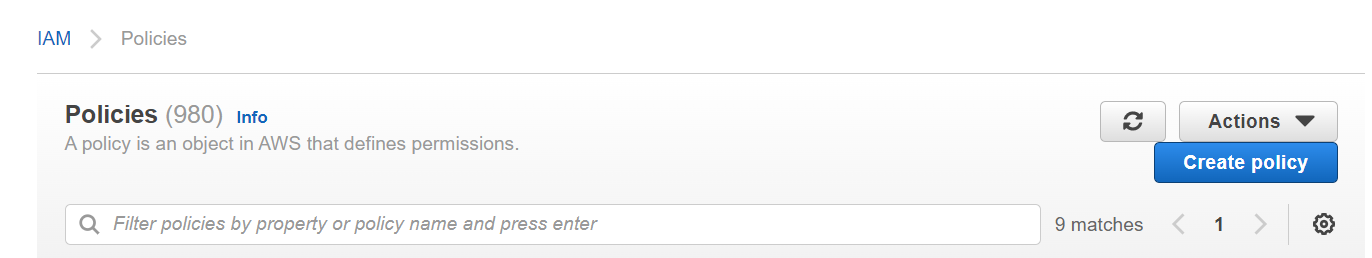
- Before creating policies we must know the organization name, Env name, Region and your Account ID. For more information on this see Introduction.
- We will create polices in order for blotout user to deploy all the required resources.