Policies¶
By default any user created in AWS doesn't have any permissions. We need to create some policies so that we can allow the user to perform certain actions in AWS. We can either chose to attach admin access or to create the following policies -
Below steps are continuation of how to attach policies to a user
Policy 1: Policy for access related to s3¶
- Click on JSON to create the policy based on JSON document.
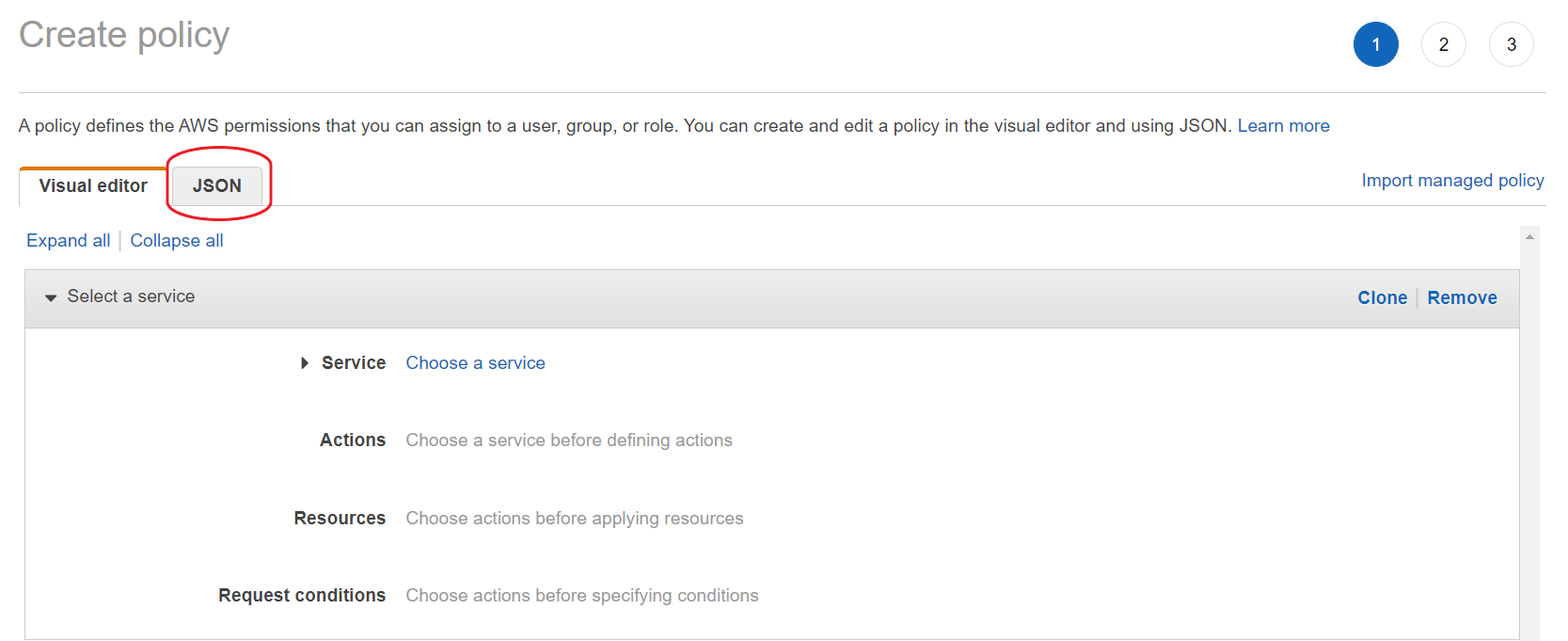
- Paste the following in the text box by replacing its original content.
- Replace
<ORG_NAME>with the Organization Name and<ENV_NAME>with the Environment name in the above JSON policy document. - Click on Next: Tags and Next: Review. You can add tags if you want.
- Name the policy as
self-serve-s3-policyand use the following image to fill in the details and then click Create Policy.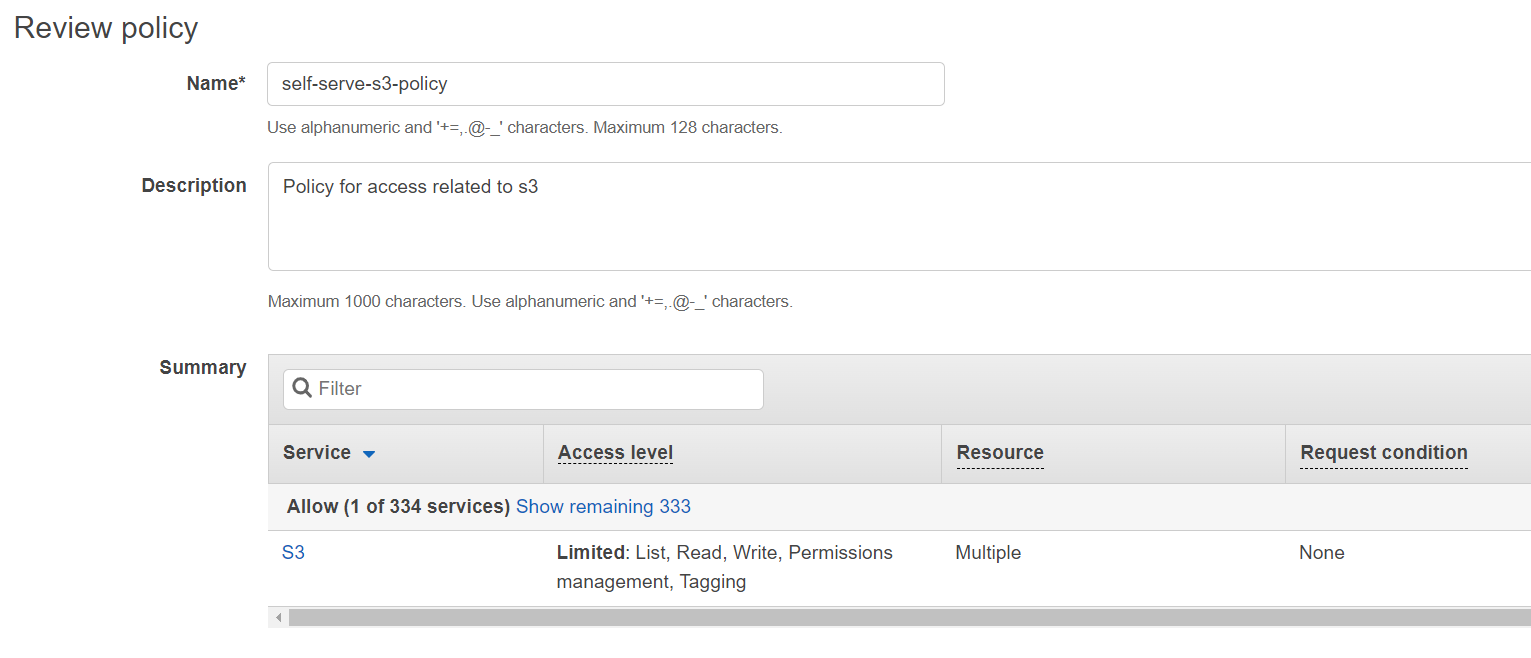
Policy 2: Policy for access related to iam¶
- Click on IAM from your console and then select Policies.
- Click on Create Policy and then click on JSON to create the policy based on JSON document.
- Paste the following in the text box by replacing its original content.
- Replace
<ACCOUNT_ID>with the Account ID. - Click on Next: Tags and Next: Review. You can add tags if you want.
- Name the policy as
self-serve-iam-policyand use the following image to fill in the details and then click Create Policy.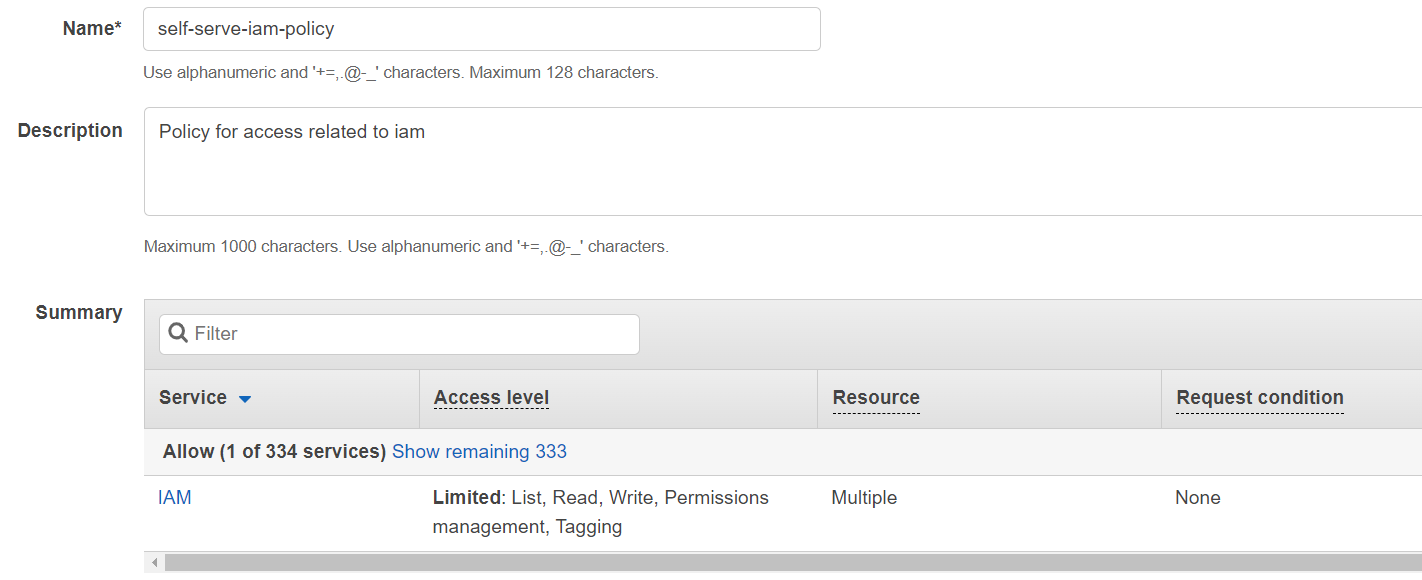
Policy 3: Policy for access related to eks¶
- Click on IAM from your console and then select Policies.
- Click on Create Policy and then click on JSON to create the policy based on JSON document.
- Paste the following in the text box by replacing its original content.
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114 115 116 117 118 119 120 121 122 123 124 125 126 127 128 129 130 131 132 133 134 135 136 137 138 139
{ "Statement": [ { "Action": [ "elasticloadbalancing:RemoveListenerCertificates", "elasticloadbalancing:AddListenerCertificates", "eks:UpdateNodegroupVersion", "eks:UpdateNodegroupConfig", "eks:UpdateClusterVersion", "eks:UpdateClusterConfig", "eks:UpdateAddon", "eks:TagResource", "eks:ListUpdates", "eks:ListNodegroups", "eks:ListAddons", "eks:DescribeUpdate", "eks:DescribeNodegroup", "eks:DescribeCluster", "eks:DescribeAddon", "eks:DeleteNodegroup", "eks:DeleteCluster", "eks:DeleteAddon", "eks:CreateNodegroup", "eks:CreateAddon", "acm:ListTagsForCertificate", "acm:ImportCertificate", "acm:DescribeCertificate", "acm:DeleteCertificate", "acm:AddTagsToCertificate" ], "Effect": "Allow", "Resource": [ "arn:aws:elasticloadbalancing:<REGION>:<ACCOUNT_ID>:listener/net/*/*/*", "arn:aws:elasticloadbalancing:<REGION>:<ACCOUNT_ID>:listener/app/*/*/*", "arn:aws:eks:<REGION>:<ACCOUNT_ID>:nodegroup/<ORG_NAME>_<ENV_NAME>/managed-node/*", "arn:aws:eks:<REGION>:<ACCOUNT_ID>:cluster/<ORG_NAME>_<ENV_NAME>", "arn:aws:eks:<REGION>:<ACCOUNT_ID>:addon/<ORG_NAME>_<ENV_NAME>/*/*", "arn:aws:acm:<REGION>:<ACCOUNT_ID>:certificate/*" ], "Sid": "" }, { "Action": [ "ec2:RevokeSecurityGroupIngress", "ec2:RevokeSecurityGroupEgress", "ec2:ReleaseAddress", "ec2:ModifyVpcEndpoint", "ec2:ModifyVpcAttribute", "ec2:ModifySubnetAttribute", "ec2:ImportKeyPair", "ec2:DisassociateRouteTable", "ec2:DetachInternetGateway", "ec2:DescribeVpcAttribute", "ec2:DeleteVpcEndpoints", "ec2:DeleteVpc", "ec2:DeleteSubnet", "ec2:DeleteSecurityGroup", "ec2:DeleteRouteTable", "ec2:DeleteRoute", "ec2:DeleteNatGateway", "ec2:DeleteKeyPair", "ec2:DeleteInternetGateway", "ec2:CreateVpcEndpoint", "ec2:CreateVpc", "ec2:CreateTags", "ec2:CreateSubnet", "ec2:CreateSecurityGroup", "ec2:CreateRouteTable", "ec2:CreateRoute", "ec2:CreateNatGateway", "ec2:CreateInternetGateway", "ec2:AuthorizeSecurityGroupIngress", "ec2:AuthorizeSecurityGroupEgress", "ec2:AttachInternetGateway", "ec2:AssociateRouteTable", "ec2:AllocateAddress" ], "Effect": "Allow", "Resource": [ "arn:aws:ec2:<REGION>:<ACCOUNT_ID>:vpc/*", "arn:aws:ec2:<REGION>:<ACCOUNT_ID>:vpc-endpoint/*", "arn:aws:ec2:<REGION>:<ACCOUNT_ID>:subnet/*", "arn:aws:ec2:<REGION>:<ACCOUNT_ID>:security-group/*", "arn:aws:ec2:<REGION>:<ACCOUNT_ID>:security-group-rule/*", "arn:aws:ec2:<REGION>:<ACCOUNT_ID>:route-table/*", "arn:aws:ec2:<REGION>:<ACCOUNT_ID>:natgateway/*", "arn:aws:ec2:<REGION>:<ACCOUNT_ID>:key-pair/<ORG_NAME>_<ENV_NAME>", "arn:aws:ec2:<REGION>:<ACCOUNT_ID>:internet-gateway/*", "arn:aws:ec2:<REGION>:<ACCOUNT_ID>:elastic-ip/*" ], "Sid": "" }, { "Action": [ "elasticloadbalancing:DescribeTags", "elasticloadbalancing:DescribeLoadBalancers", "elasticloadbalancing:DescribeLoadBalancerAttributes", "elasticloadbalancing:DescribeListeners", "elasticloadbalancing:DescribeListenerCertificates", "eks:DescribeAddonVersions", "eks:CreateCluster", "ec2:DescribeVpcs", "ec2:DescribeVpcEndpoints", "ec2:DescribeVpcClassicLinkDnsSupport", "ec2:DescribeVpcClassicLink", "ec2:DescribeSubnets", "ec2:DescribeSecurityGroups", "ec2:DescribeRouteTables", "ec2:DescribePrefixLists", "ec2:DescribeNetworkInterfaces", "ec2:DescribeNetworkAcls", "ec2:DescribeNatGateways", "ec2:DescribeKeyPairs", "ec2:DescribeInternetGateways", "ec2:DescribeAvailabilityZones", "ec2:DescribeAddresses", "ec2:DescribeAccountAttributes", "acm:RequestCertificate", "acm:ListCertificates" ], "Effect": "Allow", "Resource": "*", "Sid": "" }, { "Action": [ "elasticloadbalancing:RemoveListenerCertificates", "elasticloadbalancing:AddListenerCertificates" ], "Effect": "Allow", "Resource": [ "arn:aws:elasticloadbalancing:<REGION>:<ACCOUNT_ID>:listener/net/*/*/*", "arn:aws:elasticloadbalancing:<REGION>:<ACCOUNT_ID>:listener/app/*/*/*" ], "Sid": "" } ], "Version": "2012-10-17" } - Replace
<ORG_NAME>with the Organization Name,<ENV_NAME>with the Environment name,<REGION>with the Region and<ACCOUNT_ID>with the Account ID in the above JSON policy document. - Click on Next: Tags and Next: Review. You can add tags if you want.
- Name the policy as
self-serve-eks-policyand use the following image to fill in the details and then click Create Policy.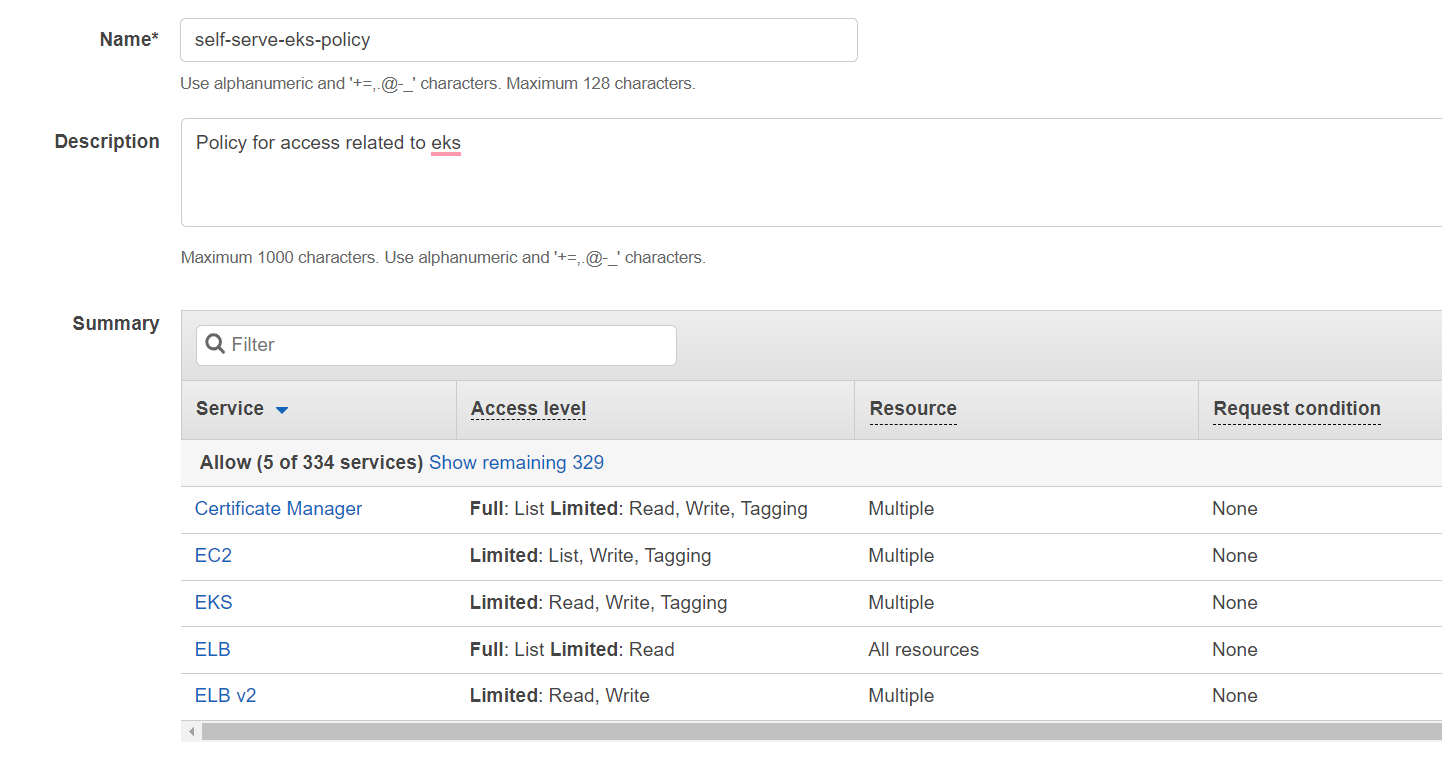
Policy 4: Policy for access related to DB¶
- Click on IAM from your console and then select Policies.
- Click on Create Policy and then click on JSON to create the policy based on JSON document.
- Paste the following in the text box by replacing its original content.
- Replace
<ORG_NAME>with the Organization Name,<ENV_NAME>with the Environment name,<REGION>with the Region and<ACCOUNT_ID>with the Account ID in the above JSON policy document. - Click on Next: Tags and Next: Review. You can add tags if you want.
- Name the policy as
self-serve-db-policyand use the following image to fill in the details and then click Create Policy.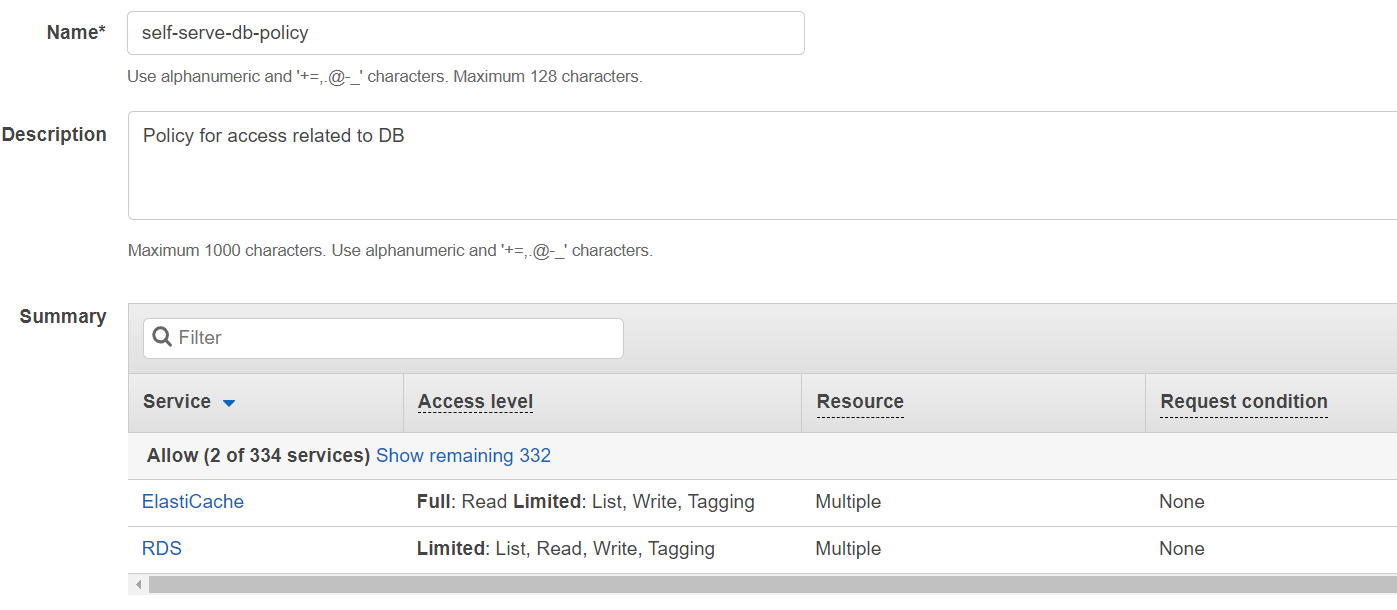
Policy 5: Policy for access related to CDN¶
- Click on IAM from your console and then select Policies.
- Click on Create Policy and then click on JSON to create the policy based on JSON document.
- Paste the following in the text box by replacing its original content.
- Replace
<ACCOUNT_ID>with the Account ID in the above JSON policy document. - Click on Next: Tags and Next: Review. You can add tags if you want.
- Name the policy as
self-serve-cdn-policyand use the following image to fill in the details and then click Create Policy.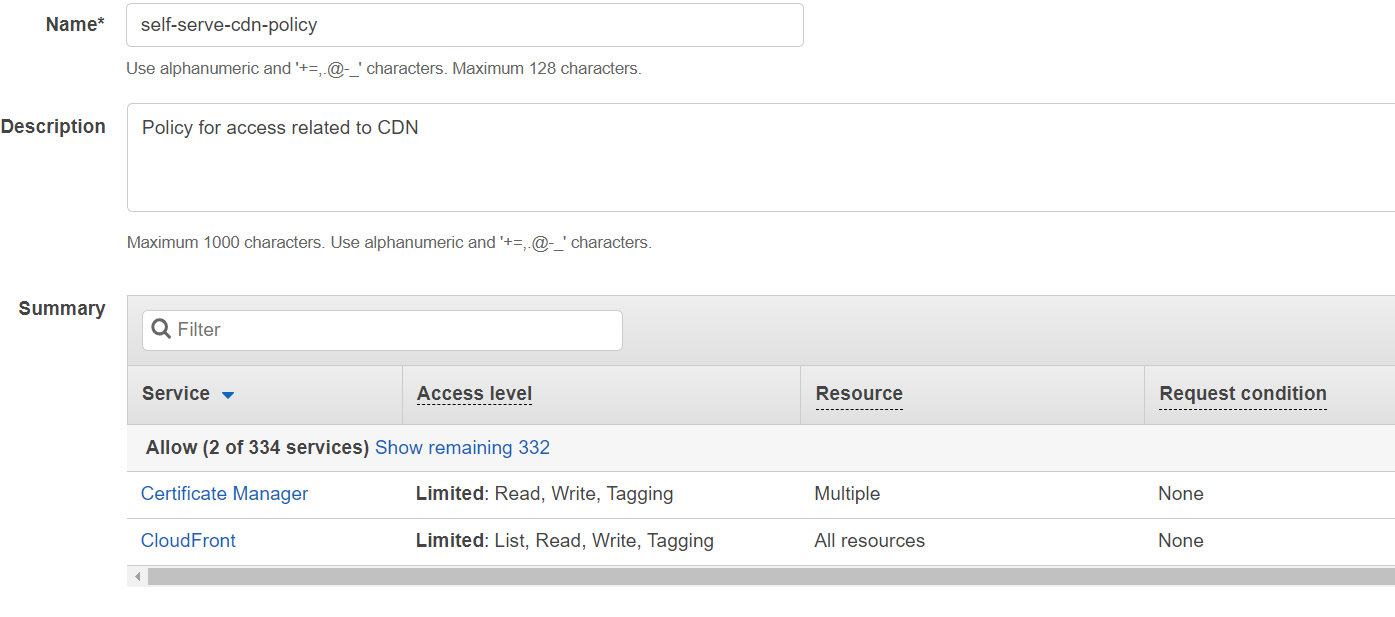
Policy 6: Policy for access related to other extra services¶
- Click on IAM from your console and then select Policies.
- Click on Create Policy and then click on JSON to create the policy based on JSON document.
- Paste the following in the text box by replacing its original content.
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114 115 116 117 118 119 120 121 122 123 124 125 126 127
{ "Statement": [ { "Action": [ "secretsmanager:PutSecretValue", "secretsmanager:GetSecretValue", "secretsmanager:GetResourcePolicy", "secretsmanager:DescribeSecret", "secretsmanager:DeleteSecret", "secretsmanager:CreateSecret", "kms:GenerateDataKey", "kms:DescribeKey", "kms:Decrypt", "kms:CreateGrant", "glue:UpdateTable", "glue:UpdatePartition", "glue:UpdateDatabase", "glue:UpdateCrawler", "glue:TagResource", "glue:StopCrawler", "glue:StartCrawler", "glue:GetTables", "glue:GetTable", "glue:GetPartitions", "glue:GetPartition", "glue:GetDatabases", "glue:GetDatabase", "glue:GetCrawler", "glue:DeleteTable", "glue:DeletePartition", "glue:DeleteDatabase", "glue:DeleteCrawler", "glue:CreateTable", "glue:CreatePartition", "glue:CreateDatabase", "glue:BatchUpdatePartition", "glue:BatchGetPartition", "glue:BatchGetCrawlers", "glue:BatchDeletePartition", "glue:BatchCreatePartition", "firehose:TagDeliveryStream", "firehose:StopDeliveryStreamEncryption", "firehose:StartDeliveryStreamEncryption", "firehose:PutRecord", "firehose:ListTagsForDeliveryStream", "firehose:DescribeDeliveryStream", "firehose:DeleteDeliveryStream", "firehose:CreateDeliveryStream", "firehose:UpdateDestination", "elasticmapreduce:DescribeStep", "elasticmapreduce:DescribeCluster", "elasticmapreduce:AddTags", "elasticmapreduce:AddJobFlowSteps", "athena:StartQueryExecution", "athena:ListTableMetadata", "athena:GetTableMetadata", "athena:GetQueryResults", "athena:ListDatabases", "athena:GetQueryExecution" ], "Effect": "Allow", "Resource": [ "arn:aws:secretsmanager:<REGION>:<ACCOUNT_ID>:secret:*", "arn:aws:kms:<REGION>:<ACCOUNT_ID>:key/*", "arn:aws:glue:<REGION>:<ACCOUNT_ID>:table/*/*", "arn:aws:glue:<REGION>:<ACCOUNT_ID>:database/*", "arn:aws:glue:<REGION>:<ACCOUNT_ID>:catalog", "arn:aws:glue:<REGION>:<ACCOUNT_ID>:crawler/*", "arn:aws:firehose:<REGION>:<ACCOUNT_ID>:deliverystream/*", "arn:aws:elasticmapreduce:<REGION>:<ACCOUNT_ID>:cluster/*", "arn:aws:athena:<REGION>:<ACCOUNT_ID>:workgroup/*", "arn:aws:athena:<REGION>:<ACCOUNT_ID>:datacatalog/*", "arn:aws:logs:<REGION>:<ACCOUNT_ID>:log-group/*", "arn:aws:logs:<REGION>:<ACCOUNT_ID>:log-group/*:log-stream/*" ], "Sid": "" }, { "Action": [ "sts:GetCallerIdentity", "sts:DecodeAuthorizationMessage", "route53:AssociateVPCWithHostedZone", "glue:StartCrawlerSchedule", "glue:ListCrawlers", "glue:GetCrawlers", "glue:GetCrawlerMetrics", "glue:CreateCrawler", "firehose:ListDeliveryStreams", "elasticmapreduce:RunJobFlow", "elasticmapreduce:ListSecurityConfigurations", "elasticmapreduce:ListClusters", "elasticmapreduce:DescribeSecurityConfiguration", "elasticmapreduce:CreateSecurityConfiguration", "ce:GetCostAndUsage", "logs:CreateLogGroup", "logs:DescribeLogGroups", "logs:ListTagsLogGroup", "logs:DeleteLogGroup", "logs:CreateLogStream", "logs:DescribeLogStreams", "logs:DeleteLogStream", "SNS:CreateTopic", "events:PutRule", "events:DescribeRule", "SNS:SetTopicAttributes", "SNS:GetTopicAttributes", "events:ListTagsForResource", "SNS:ListTagsForResource", "SNS:DeleteTopic", "events:PutTargets", "SNS:Subscribe", "events:ListTargetsByRule", "SNS:GetSubscriptionAttributes", "cloudwatch:PutMetricAlarm", "cloudwatch:DescribeAlarms", "cloudwatch:GetMetricData", "cloudwatch:ListMetrics", "cloudwatch:ListTagsForResource", "cloudwatch:DeleteAlarms" ], "Effect": "Allow", "Resource": "*", "Sid": "" } ], "Version": "2012-10-17" } - Replace
<REGION>with the Region and<ACCOUNT_ID>with the Account ID in the above JSON policy document. - Click on Next: Tags and Next: Review. You can add tags if you want.
- Name the policy as
self-serve-extra-policyand use the following image to fill in the details and then click Create Policy.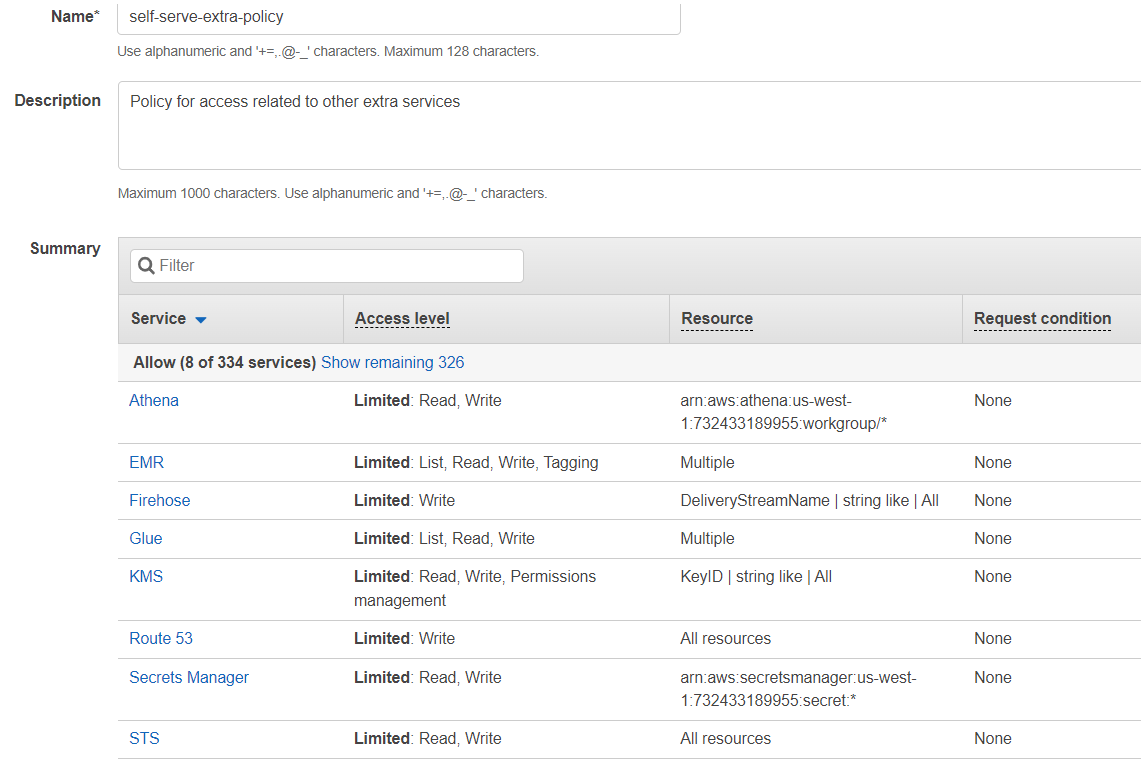
Attaching policies to the IAM user¶
- Go to console and click on IAM.
- Click on Users and then click on the user you created in the previous step. Taking the previous example name of the user is
blotout. - Click on Add Permissions to attach the permissions to the user
blotout.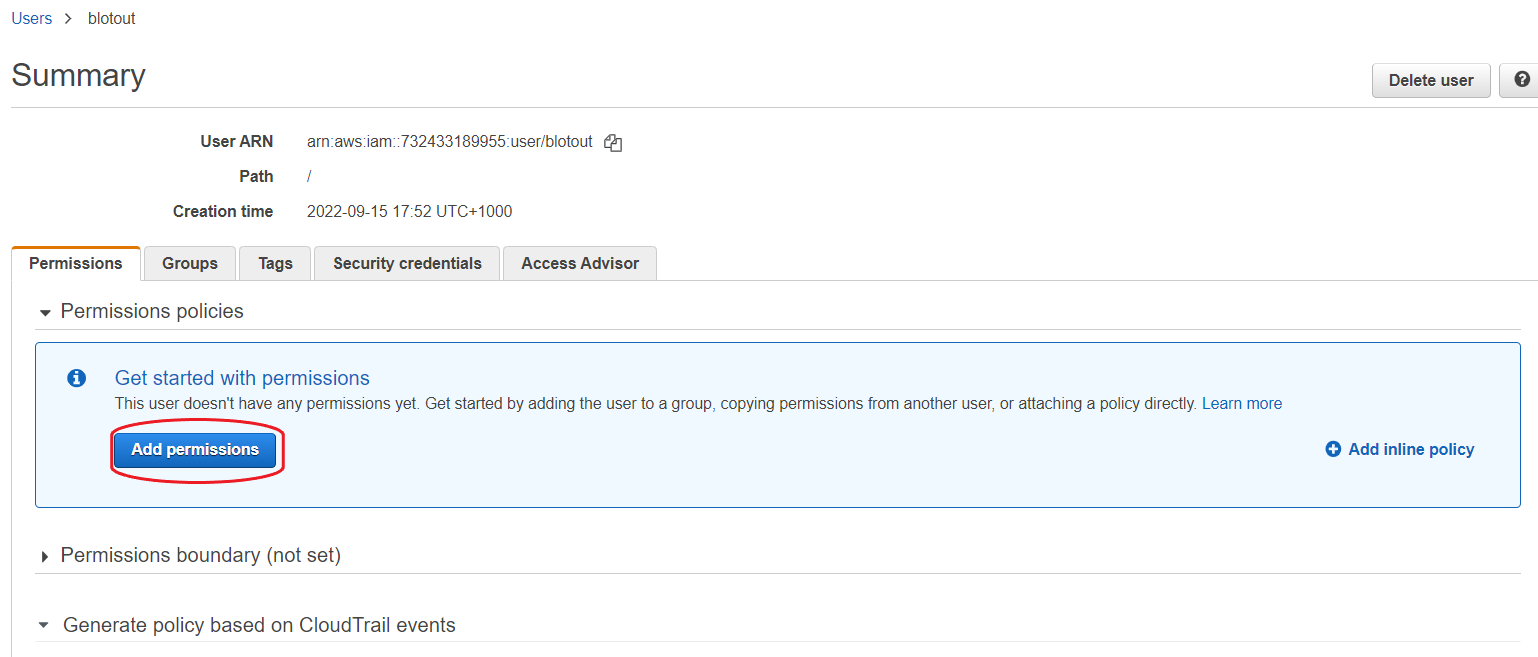
- Click on Attach existing policies directly and then filter the policies by searching self-serve. Select all the policies that we created above.
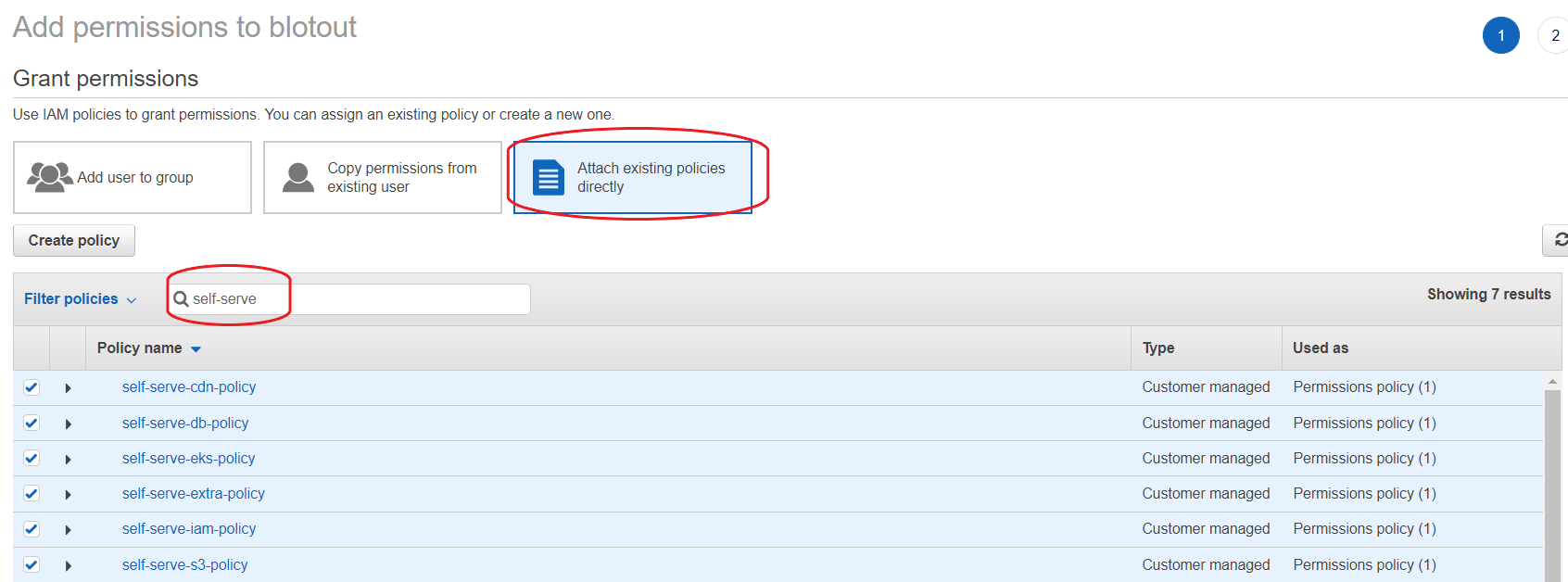
- Click on Next: Review and then Add Permissions.
- Your user (user credentials) now has the required permissions.